Redefining Privileges for Non-Administrative Windows Users

Redefining Privileges for Non-Administrative Windows Users
By default, standard users on Windows can run programs with elevated privileges if they enter an administrator password when prompted by User Access Control (UAC).
However, this is not the only behavior that the UAC has for standard user accounts, and you can change it depending on how secure these accounts are and the environment the computer is in. We’re going to show you how.
The UAC Behaviors Available for Standard User Accounts
Unlike when changing UAC behaviors for administrator accounts , the behaviors for standard user accounts are a little more limited. According to the Microsoft Learn website, here are the behaviors you can choose and what they mean:
- Automatically deny elevation requests: This option returns an Access denied error message to standard users when they try to perform an operation that requires elevation of privilege. Most organizations that run desktops as standard users configure this policy to reduce help desk calls.
- Prompt for credentials on the secure desktop: When an operation requires elevation of privilege, the user is prompted on the secure desktop to enter a different username and password. If the user enters valid credentials, the operation continues with the applicable privilege.
- Prompt for credentials: An operation that requires elevation of privilege prompts the user to type an administrative username and password. If the user enters valid credentials, the operation continues with the applicable privilege.
The default UAC behavior for standard user accounts is Prompt for credentials, but Microsoft recommends you change it to Automatically deny elevation requests. That way, only users with administrator accounts can decide how the UAC behaves and make choices that will keep the computer safe.
How to Change the UAC Behavior for Standard Users in the Local Group Policy Editor
The easiest way to change the way UAC behaves for standard users is to tweak the User Account Control: Behavior of the elevation prompt for standard users policy. To do that, open the Local Group Policy Editor and follow the steps below.
The Local Group Policy Editor isn’t available by default on Windows Home. As such, check out how to access the Group Policy Editor on Windows Home before continuing.
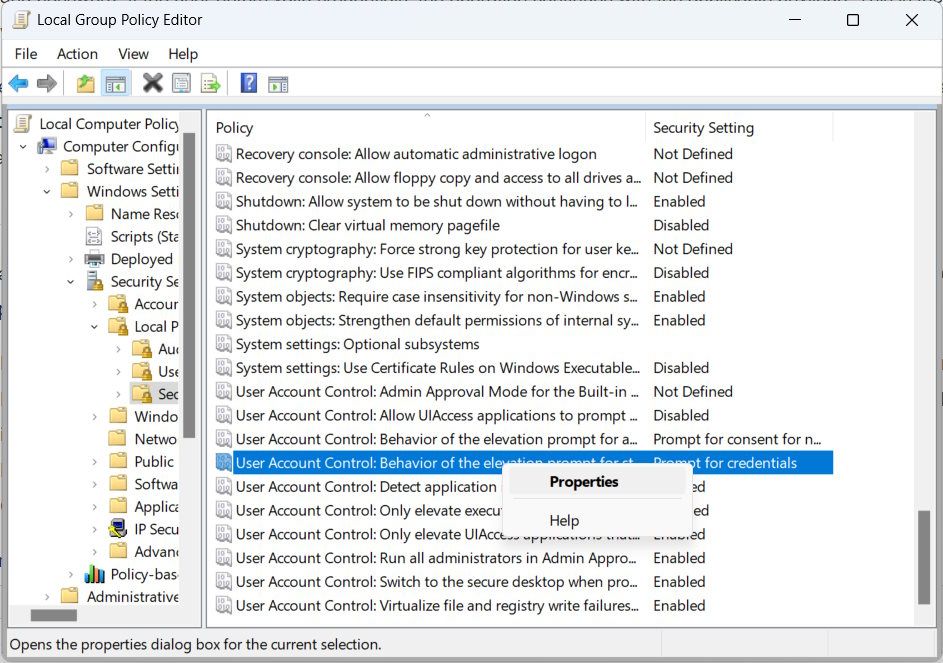
- Head to Computer Configuration > Windows Settings > Security Settings > Local Policies > Security Options.
- Right-click the User Account Control: Behavior of the elevation prompt for standard users policy and select Properties in the menu.

- Expand the dropdown and choose a different UAC behavior.
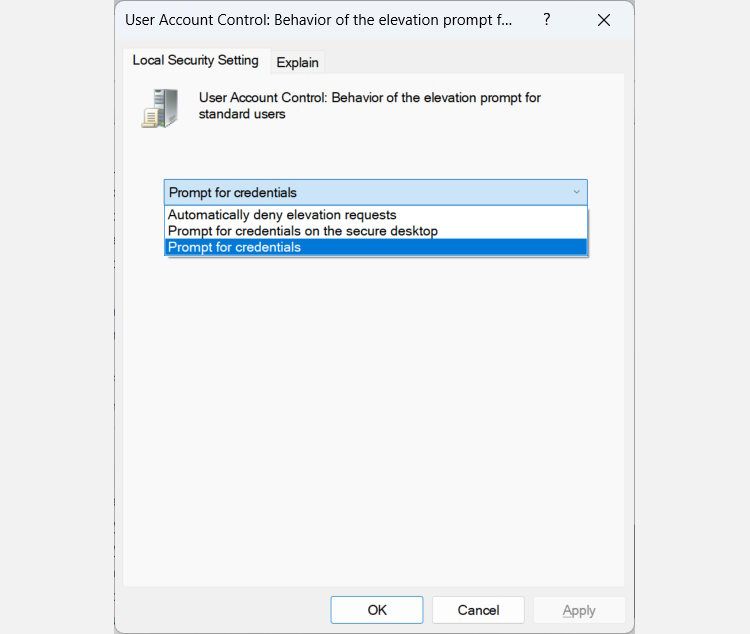
4. Click OK.
Keep in mind that only administrators can change the behavior of the UAC. If a standard user tried to change it using the Local Group Policy Editor, for example, they’d probably get an Access denied error message.
How to Change the UAC Behavior for Standard Users in the Registry Editor
If you’re looking for another way to change UAC behavior for standard users, or the Local Group Policy is not working on your computer, you can make changes in the Windows registry instead.
Before you do that, however, we recommend you create a system restore point to protect your computer in case you make a mistake. Once you do that, open the Registry Editor and follow the steps below:
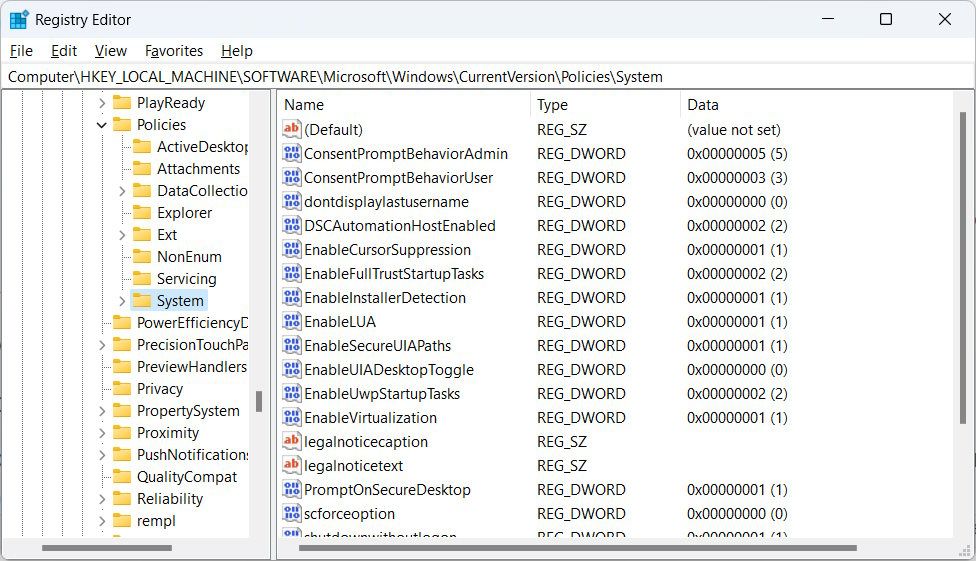
Copy HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System and paste it into the address bar at the top of the Registry Editor.

Press Enter on your keyboard to go to the System key.
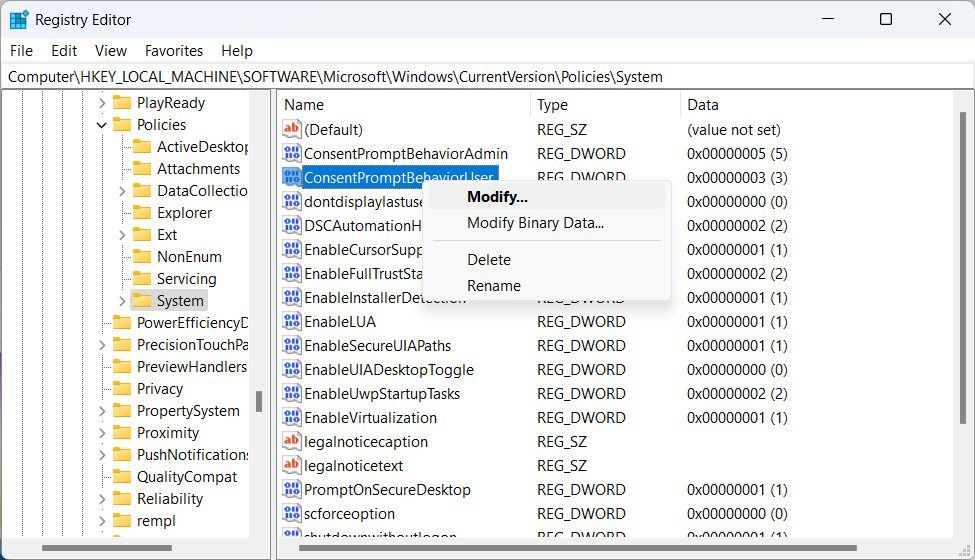
Right-click the ConsentPromptBehaviorUser value in the right panel and select Modify.

In the Value data text box, enter 0 for Automatically deny elevation requests, 1 for Prompt for credentials on the secure desktop, or 3 for Prompt for credentials.
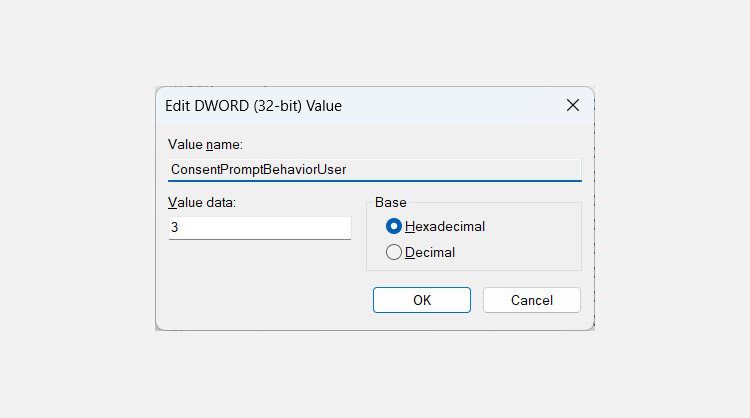
5. Click OK.
Now restart your computer to allow the changes to take effect.
Control UAC’s Behavior for Standard Users on Windows
UAC is an integral part of protecting your Windows computer from malicious programs that want to run with elevated privileges. While you can’t make it elevate programs without prompting, you can make it stricter by setting it to Automatically deny elevation requests. And, as you can see, it is quite easy to do, whether you’re using the Local Group Policy Editor or the Registry Editor.
However, this is not the only behavior that the UAC has for standard user accounts, and you can change it depending on how secure these accounts are and the environment the computer is in. We’re going to show you how.
Also read:
- [New] 2024 Approved Best Video Player Apps for Windows Phone
- [New] 2024 Approved Expanding Digital Presence Stream to YouTube + Additional Platforms
- [New] The Art of Capture and Storage Managing Snapshots Like a Pro
- [New] YouTube's Best 10 Cutting-Edge Reaction Ideas
- Altering WinTerral's Visual Theme
- Compact Sound Sensation in the World of MP3 Players
- Easy Ways to Revert Personalized Settings on Windows 11'S Search
- Fake the Location to Get Around the MLB Blackouts on Xiaomi Redmi 12 5G | Dr.fone
- Fix Self-Shutdowns: Steps for Windows 11 Users
- In 2024, Easiest Guide How to Clone Honor X50 Phone? | Dr.fone
- Restoring Disconnected Windows Printer Linkup
- Smoothing Over Elan's Operational Snags in Win10
- Solve iCloud Download Issues with These Helpful Steps
- Systematic Approach to Eliminate Flashing on Windows
- The Essential Guide to Brightening the Windows 11 Pointer
- Top Hashtags on Instagram: Boost Your Visibility
- Unlock Frozen Windows-Handbraked Vaults
- Updated 2024 Approved Ultimate Guide to Selecting Mobile Speech-to-Text Software
- Windows 11'S High Dynamic Range Mastered for the Modern User
- Title: Redefining Privileges for Non-Administrative Windows Users
- Author: Joseph
- Created at : 2025-02-23 00:36:05
- Updated at : 2025-03-01 17:36:47
- Link: https://windows11.techidaily.com/redefining-privileges-for-non-administrative-windows-users/
- License: This work is licensed under CC BY-NC-SA 4.0.